Tour button
Focus on Security: Preparing your Operations
“Attraction Security Guidance” and new “Takeover” Resources

Every year the social landscape of our guests and employees changes with new trends and challenges that operators will need to address. Recently operators have worked through social takeovers and drone intrusions which are becoming more common threats. The last few years have also seen changing political landscapes and unexpected wars impact operations.
As IAAPA kicks off Safety and Security Month in May with multiple education events to support your operations, the IAAPA global and regional Safety and Security Committees want to start with a conversation about security. How is your facility preparing for this season’s challenges and if an unexpected security situation arose, what procedures do you have in place to manage the response to the security situation? How are you identifying growing threats like social takeovers, which can impact operations and cause security incidents, and updating your security programs for that scenario?
For those who work in safety and security, we know that incidents are going to occur. We look at prior incidents as a reference and work to predict what could happen - knowing we cannot predict or prevent every scenario we build detection and response plans. For those focused on security, having a strong prevention and detection plan in conjunction with a robust response and recovery plan builds a security resilient organization.
Highlighting best practices from the IAAPA “Visitor Attraction Security Guidance - 10 Point Review Plan” and the new IAAPA “SOCIAL TAKEOVERS: Best Practice to Combat” resources, now is the time to evaluate where you are and how to improve your organization’s security resiliency.
Prevention and Detection
- Identify Security Vulnerabilities
Perform a security risk assessment and facility audit to identify potential vulnerabilities and weak points in your physical and digital security protections. Ensure to include people as part of the assessment and audit because people are often your weakest links. From your findings you can create a plan to reduce the impact or prevent the occurrence of a security incident.
- Promote Strong Security Culture
The security of your facility is every employee’s responsibility. From back-of-house security to front-of-house security, ensuring that authorized people are only in permitted locations is critical. Promote a culture of eye contact and awareness of who is in your surroundings. Employees are empowered to politely ask when they see someone unknown or someone who looks out of place: “You look a little lost, how many I help you?” or “I am sorry, I do not recognize you, may I see your identity badge?”.
- Utilize a ‘See Something, Say Something’ Program with Employees and Guests
Empowering everyone to report suspicious behaviors or objects increases the likelihood of detection before an incident escalates. What is your reporting process, and does it include ability to receive information from employees and guests? What training and signage are used to educate about the program? How frequently do you conduct refresher training with employees?
- Proactive Threat Monitoring
Knowledge of an impending security threat affords you the opportunity to prepare. Sometimes minutes or hours of notice can enable teams to drastically reduce the impact. Either employ in-house security professionals or an external security contractor to monitor for threats via social media or news sources. Developing a relationship with your local law enforcement teams is also critical as they have advanced monitoring capabilities and can alert your facility of possible threats. For example, social takeovers are coordinated on social media and a facility could gain advance notice if one has been schedule at your location. Empowering your younger generation staff who are more social media active to report what they see online in regard to your facility is an example of expanding your in-house ‘security alert team’.
Response and Recovery
Create and Review Response and Recovery Plans
Different scenarios require different planning. Plans should address internal and external communications especially with local law enforcement, threat containment, medical response, operational procedures including search plans, securing perimeter control and critical infrastructure, disciplinary policies, and recovery procedures. Table-top exercises are an excellent method to test plans, identify improvement areas and provide employee training.
Examples of scenarios to review: assault/fights, riots, social takeovers, physical security breach/trespassing, cybersecurity hack, theft, drone intrusion, bomb threat, human attack by weapon, active shooter, vehicle ramming, facility attack by foreign object (drone or missile), loss of utilities (electricity and water), and fire.
Quoting Dr. Neil Dwyer from the March/April 2026 edition of Funworld Safety Corner article: “Operators that invest in structured planning, realistic training, and joint exercises with emergency services are far better positioned to manage the incidents effectively.” Dr. Dwyer, current chair of the IAAPA Global Safety and Security Committee, conducted interviews with multiple theme park operators to identify best practices for crisis management and emergency response. Planning, training, and developing partnerships with local emergency services rose to the top as effective best practices. Another important factor was the actions taken within the first minutes after an incident occurs, when your facility is managing response before the emergency services arrive. How you respond in those minutes impacts the severity of the incident. Dr. Dwyer maps out those “First X Minutes” as: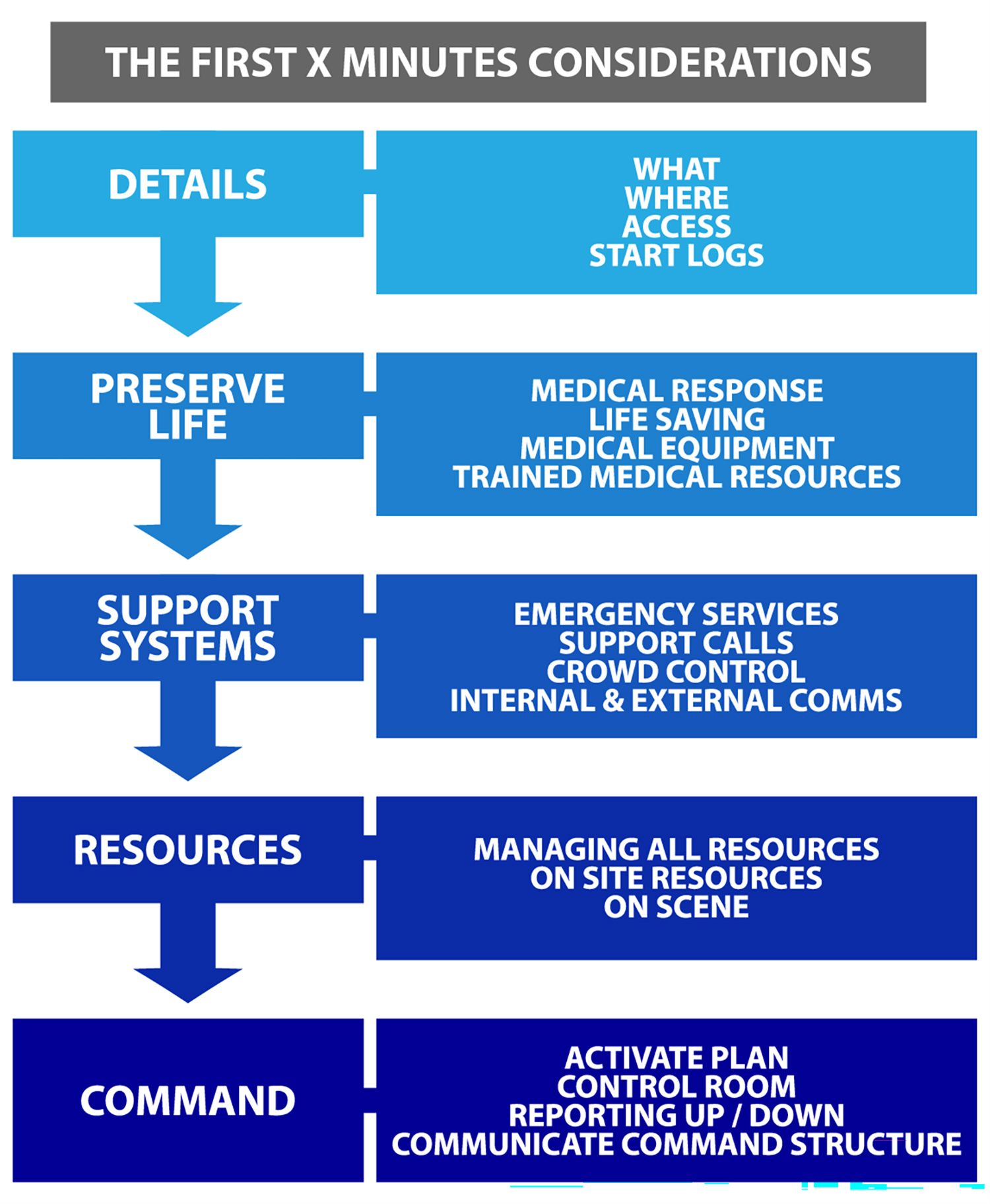
Dwyer, N. W. E. (2025) Exploring Crisis Management and Emergency Response in Theme Parks. DBA, University of Lancashire, UK, Preston.
When creating your response plans, ensure you are detailing how you respond in those first minutes because that time is often the most chaotic and could be unknown how long until emergency support arrives.
- Educate Employees and Guests to exercise ‘Run, Hide, Tell’
How do you guide your employees and guests to react during a live security threat? The UK ‘Run, Hide, Tell’ program is an example of how to reduce injuries during a live threat.
- Utilize Emergency ‘Grab Bags’
In the case of facility evacuation, prepared collection of information will be critical to continue or recover operations. Where are your building and facility technical drawings, details of utility or hazardous shut-off points, emergency contact information and other key information which could be needed during a security incident? Employees should be trained on what information has been gathered and how to access the information if evacuated off-site. Printed copies of information with off-site resources is an excellent option. Other items to have readily accessible in an emergency ‘grab bag’ are first aid kits, high-visibility and protective clothing, light sources, megaphones, and master keys. What else would you need from your office if you could not access your office?
Building out your security program is a constant journey with review and refinement, especially as the security threats and challenges change.
Want to continue this conversation with industry professionals? Join the Safety and Security Committee Live Chat on May 7, 2026, and the webinar “Social Takeover – Learn Best Practices to Combat on May 14, 2026. See the IAAPA events calendar to register for the events.
The security guides and other industry security information can be found on IAAPA Security Resources.
Follow IAAPA for news and event announcements in your favorite social media apps
Connect with the Real Stories Behind the Fun
Follow our social media for authentic stories, special moments, and behind-the-scenes looks from the attractions world.